Netgear GS418TPP User Manual - Page 349
Sequence Number, Action, Permit, Egress Queue, Logging, Enable, Match Every, Disable, Mirror Interface
 |
View all Netgear GS418TPP manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 349 highlights
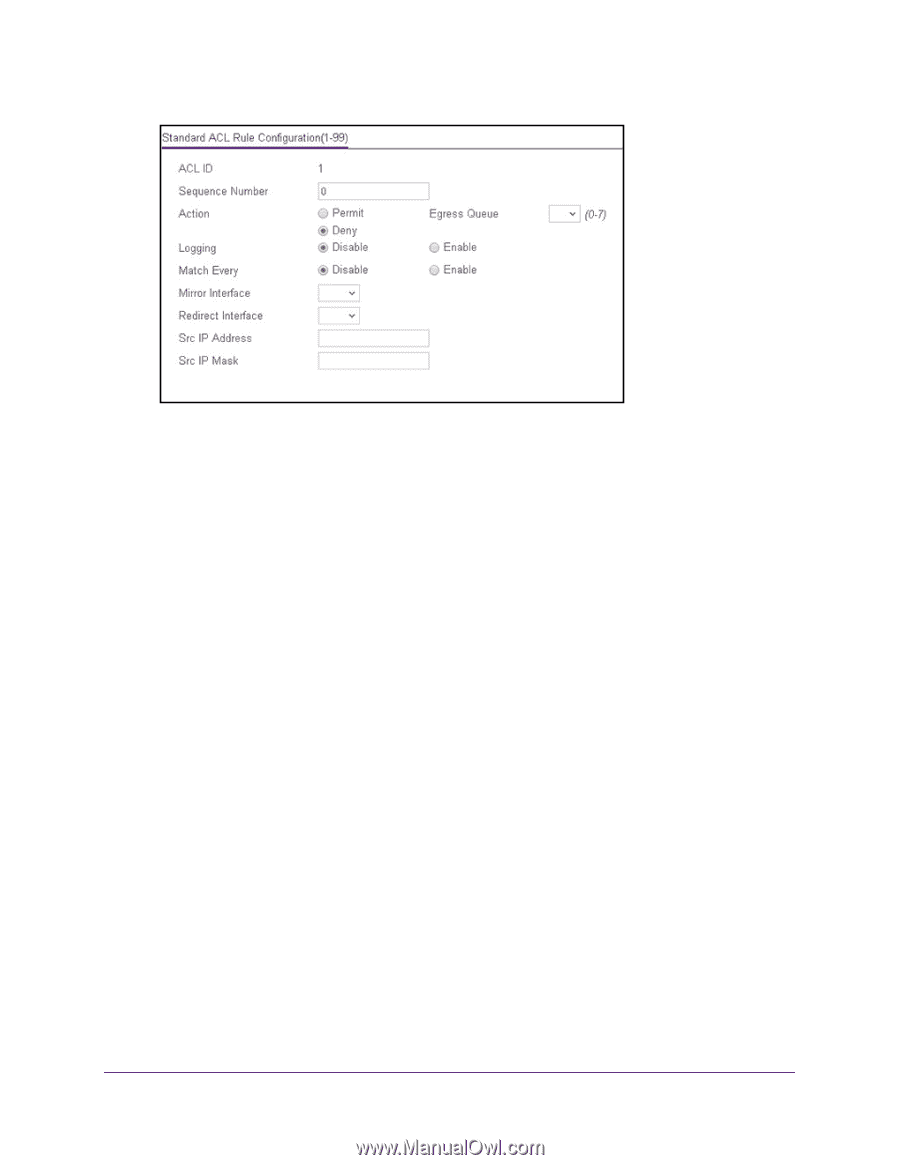
ProSAFE 8-Port or 16-Port Gigabit Smart Managed Switch Model GS418TPP, GS510TLP, and GS510TPP 8. Specify the following match criteria for the rule: • Sequence Number. Enter an ACL sequence number in the range of 1 to 2147483647 that is used to identify the rule. An IP ACL can contain up to 50 rules. • Action. Select the ACL forwarding action, which is one of the following: - Permit. Forward packets that meet the ACL criteria. - Deny. Drop packets that meet the ACL criteria. • Egress Queue. If the selection form the Action menu is Permit, you can specify the hardware egress queue identifier that is used to handle all packets matching this IP ACL rule. The range of queue IDs is 0 to 7. • Logging. If the selection form the Action menu is Deny, you can enable logging for the ACL by selecting the Enable radio button. (Logging is subject to resource availability in the device.) If the access list trap flag is also enabled, periodic traps are generated, indicating the number of times this rule was evoked during the report interval. A fixed five-minute report interval is used for the switch. A trap is not issued if the ACL rule hit count is zero for the current interval. • Match Every. From the Match Every menu, select whether all packets must match the selected IP ACL rule: - Enable. All packets must match the selected IP ACL rule and are either permitted or denied. - Disable. Not all packets need to match the selected IP ACL rule. • Mirror Interface. From the Mirror Interface menu, select the specific egress interface to which the matching traffic stream must be copied, in addition to being forwarded normally by the switch. This field cannot be set if a redirect interface is already configured for the IP ACL rule. This field is visible for a Permit action. Manage Device Security 349